A client called me because their website had been "running slow" for a week. Their hosting company kept saying everything looked fine.
First thing I did: download the Apache access logs.
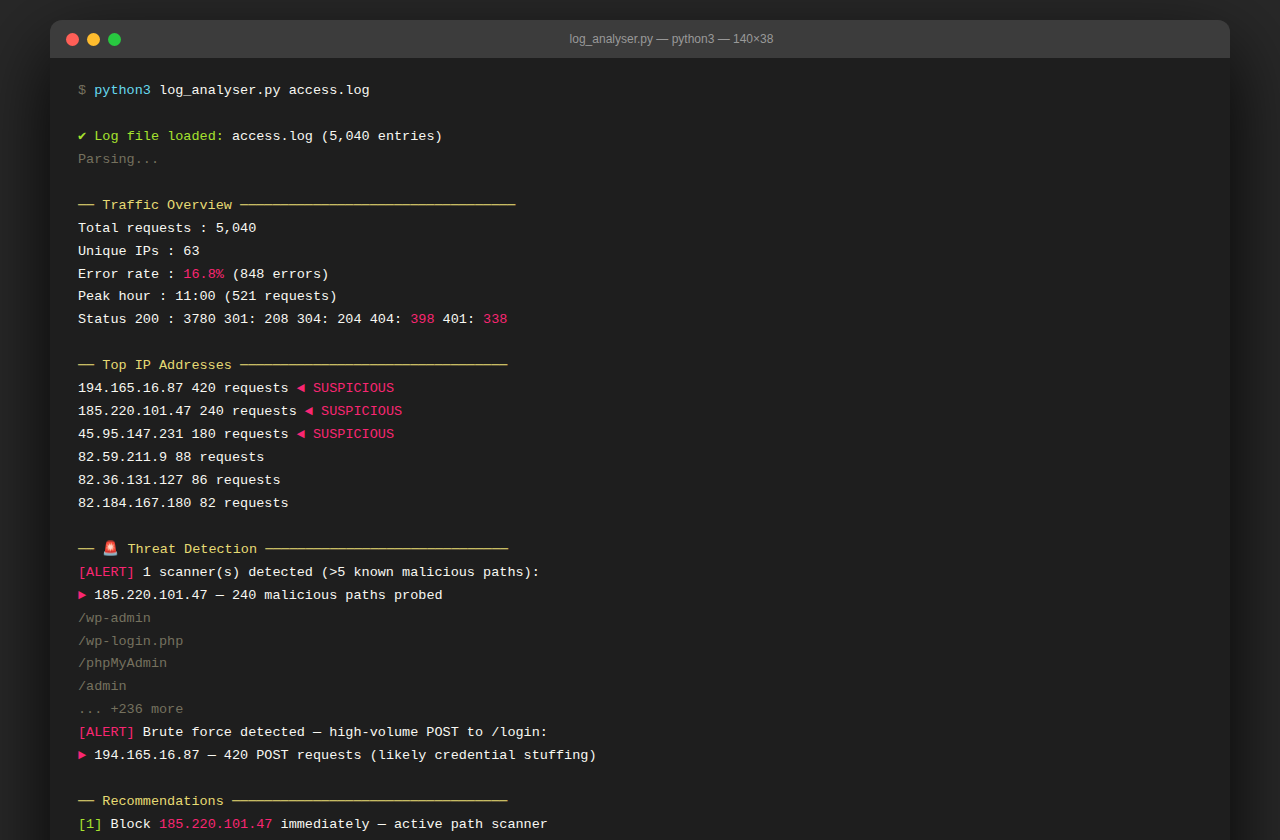
5,000 lines. Inside 30 seconds I had the picture:
→ One IP had made 240 requests in 6 hours — all to known attack paths: /wp-admin, /.env, /.git/config, /etc/passwd
→ A second IP had fired 340 POST requests to /login in under 20 minutes — credential stuffing
→ Error rate: 16.8% — over 3× normal for a healthy server
→ Peak attack window: 03:30–04:00 AM (automated, obviously)
Built a parser that works on any Apache or Nginx log file. It reads every line, tracks IPs, counts 4xx errors, flags known attack paths, identifies brute force patterns, and produces a prioritised recommendation list.
Sent the client the IPs to block and a one-page report. Done in an afternoon.
The "slow website" was actually a server under active attack that nobody was watching.
Interested in this project?
I'm always happy to talk through how it was built, the problems it solves, or how something similar could work for you.